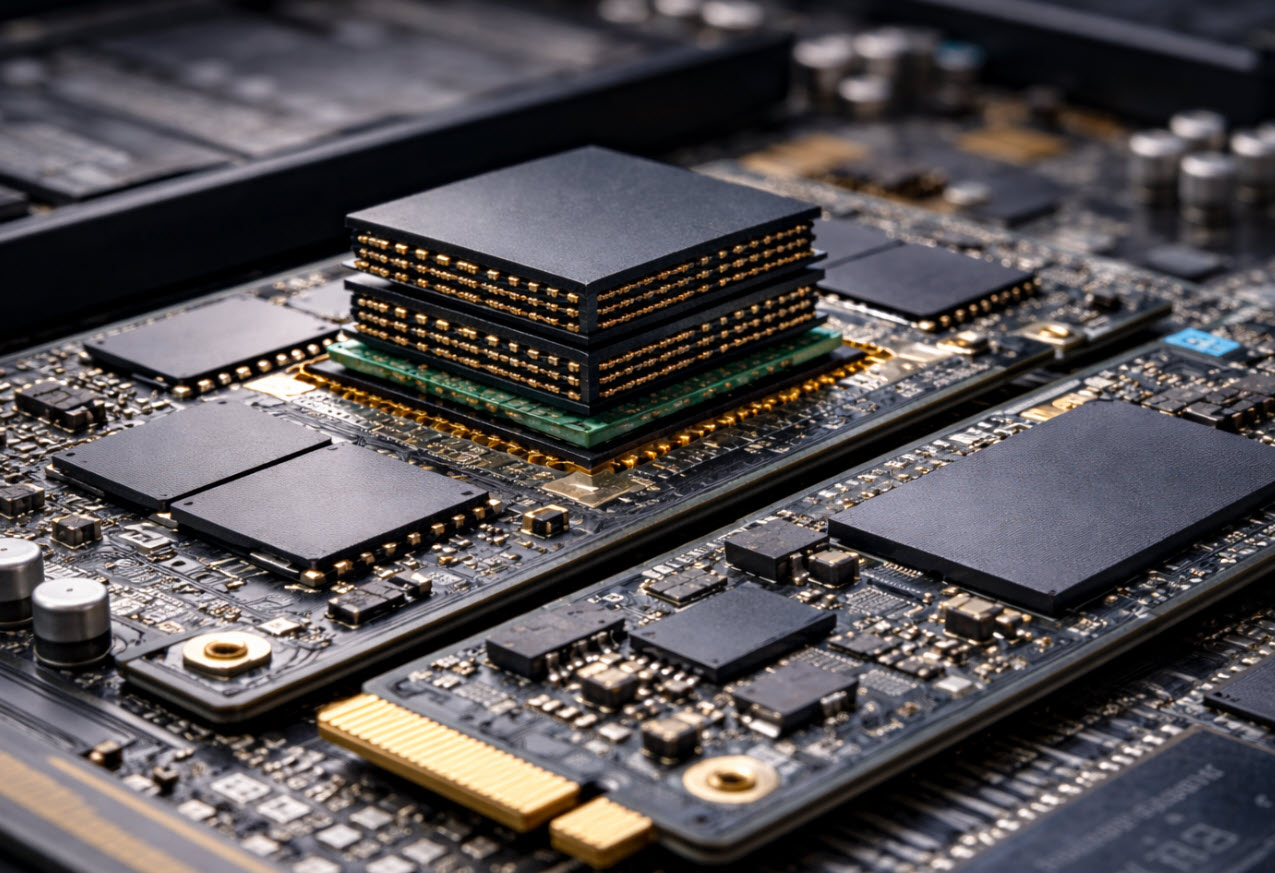
HBM vs HBF — Why the Memory Hierarchy Is Being Stretched
If you strip away the marketing language, the AI hardware race right now is about one thing: moving data is expensive. Not financially. Electrically. Every time information leaves memory, crosses a bus, hits a processor, and comes back, energy gets burned. At scale, that energy becomes heat. Heat becomes infrastructure. Infrastructure becomes cost. That’s why […]
Read Featured Analysis